Introduction
Technology has evolved from a back-office function to one of the most consequential — and risk-laden — components in modern M&A transactions. Yet 53% of dealmakers discover critical cybersecurity issues only after closing, triggering costly remediation and governance challenges.
When acquirers treat technology as secondary diligence, they inherit technical debt, security vulnerabilities, disputed IP ownership, and integration complexities that erode returns and derail synergy capture.
The stakes are quantifiable. The global average cost of a data breach reached $4.88 million in 2024, while unaddressed technical debt causes operational disruptions in 70% of deals.
Verizon's $350 million price reduction for Yahoo — disclosed after a massive unreported breach — shows how technology risks translate directly into valuation adjustments. Technology integration issues account for roughly 30% of failed mergers, which is why structured tech diligence belongs at the centre of every deal process.
This guide provides a structured framework for conducting technology due diligence in M&A. You'll learn what technology DD entails, a five-area evaluation checklist, the step-by-step assessment process, critical red flags that derail deals, and how findings shape purchase price adjustments, earn-outs, and integration planning.
TLDR:
- Technology DD systematically assesses infrastructure, security, IP, codebase quality, and integration readiness to validate the deal thesis
- 53% of acquirers discover cyber issues post-close; 70% face disruption from technical debt — both preventable with structured diligence
- Five core areas cover Infrastructure & Cloud, Security & Compliance, Software Quality & IP, AI/ML Capabilities, and Engineering Team & Vendors
- Findings directly inform purchase price adjustments, earn-out structures, and indemnification clauses
- Parallel workstreams with legal and financial DD, running 3-10 weeks depending on target complexity
What Is Technology Due Diligence in M&A?
Technology due diligence is the systematic assessment of a target company's technology assets, infrastructure, engineering capabilities, and digital risk. Tech DD validates whether the technology foundation genuinely supports the deal's investment thesis — whether that thesis centers on acquiring a scalable SaaS platform, integrating manufacturing systems, or capturing data-driven competitive advantages.
While financial due diligence evaluates balance sheets and legal DD assesses contracts and liabilities, technology DD answers distinct questions: Can this platform scale without costly rewrites? Is the intellectual property cleanly owned? What will it actually cost to maintain, secure, or integrate these systems post-close?
Why Technology DD Matters in Modern Acquisitions
Rigorous technology DD delivers three commercially critical outcomes:
- Accurate asset valuation: SaaS M&A hit its highest recorded level in 2025, accounting for 58% of total software M&A activity. In these deals, technology assets drive the majority of identifiable intangible value. Without assessing code quality, architecture scalability, and technical debt, acquirers risk overpaying for platforms that require immediate capital investment post-close.
- Early liability identification: Security gaps, open-source license violations, and unpatched vulnerabilities are quantifiable risks — not hypothetical ones. 2025 transaction audits found open-source components in 100% of deals reviewed, with license conflicts in 94% and unpatched vulnerabilities in 97%. Surfacing these during diligence allows buyers to negotiate price adjustments, establish indemnification provisions, or tie earn-outs to remediation milestones.
- Realistic integration planning: Only 14% of M&A respondents report significant success across strategic, operational, and financial integration measures. Technology DD uncovers single points of failure, vendor dependencies, and architectural incompatibilities that directly shape the post-close 100-day plan — giving acquirers a clear view of where immediate investment is needed and where talent retention is critical.

The Technology Due Diligence Checklist: 5 Core Evaluation Areas
This structured framework applies across deal types—full acquisitions, carve-outs, minority stakes—and target profiles, from pure technology companies to tech-enabled enterprises. Scope and depth vary based on investment thesis, but these five areas form the baseline assessment.
Infrastructure, Architecture, and Cloud
Modern platforms must scale without architectural rewrites. Assess whether infrastructure is cloud-native, hybrid, or legacy on-premises, and whether cloud costs scale predictably with revenue.
Key evaluation dimensions:
- Architecture scalability: Can the system handle 10x user growth without fundamental redesign?
- Cloud deployment model: 73% of organizations operate hybrid environments; 49% of production workloads remain on-premises. Understand the distribution and migration risk.
- Infrastructure resilience: Identify single points of failure, disaster recovery capabilities, and whether backup systems are tested regularly.
- FinOps maturity: Structured FinOps programs reduce cloud spend by 20–40%. Evaluate whether the target has cost governance in place or is overprovisioned.
Critical sub-checks:
- Deployment frequency and automation maturity (use DORA metrics: deployment frequency, lead time, change failure rate)
- Over-reliance on legacy hardware or unsupported platforms
- Whether DevOps practices exist in practice or only on paper
Infrastructure findings set the stage for the next layer of scrutiny. Security and regulatory exposure carry the highest deal-termination risk of any evaluation area.
Security, Compliance, and Data Privacy
Cybersecurity problems delay 62% of M&A deals, and 73% of dealmakers would walk away if undisclosed breaches were discovered. Security posture requires evidence that controls are implemented, monitored, and tested—not merely documented.
Security posture assessment:
- History of breaches or incidents, and adequacy of incident response
- Access control policies (role-based, least privilege, multi-factor authentication)
- Penetration testing frequency and remediation timelines
- Vulnerability management programs and patch cadence
Regulatory compliance obligations:
- GDPR (EU): The Dutch DPA fined Uber €290 million in 2024 for improper data transfers without Standard Contractual Clauses
- HIPAA (US): HHS settled with MedEvolve for $350,000 after unsecured PHI exposure
- PCI DSS v4.0: Mandatory compliance as of April 1, 2024; future-dated requirements enforceable by March 31, 2025
- India DPDP Act 2023: Establishes permissive cross-border data transfer rules unless restricted by government order
Cross-border transactions require mapping which regulations apply to the combined entity and identifying gaps that create post-close liability, particularly when buyer and seller operate under different regulatory regimes. Unresolved gaps become the acquirer's liability on day one of close.
Software Quality, IP Ownership, and Licensing
Poor engineering hygiene inflates post-close IT costs and slows integration. Clean IP ownership is non-negotiable; disputed or undocumented IP can block deal closing entirely.
Codebase quality evaluation:
- Volume of technical debt (measured via SQALE methodology, which quantifies both remediation cost and the business impact of leaving debt unresolved)
- Development practices: version control, code review processes, automated testing coverage, release cadence
- Documentation quality and knowledge concentration risk
IP ownership is where deals quietly unravel. The contractual hygiene around software rights is often less rigorous than founders assume.
Intellectual property verification:
- Confirm the company owns all core software, not individual employees or contractors
- Review employee and contractor IP assignment agreements (PIIAs)
- Under US law, the creator owns IP unless assigned in writing; missing assignment agreements have derailed transactions worth multiples of the cost to fix them
Open-source license compliance:
- Document all OSS dependencies and license types
- Identify copyleft licenses (GPL, AGPL) that impose derivative work obligations
- Flag unpatched vulnerabilities (97% of M&A audits find them)
AI, Machine Learning, and Emerging Technology Stack
Buyers increasingly pay premiums for AI capabilities. The critical question is whether those capabilities are genuinely proprietary or simply licensed access to third-party models with a custom interface on top.
AI/ML capability assessment:
- Proprietary vs. API-dependent: Anthropic, OpenAI, and Google control almost 90% of the enterprise LLM market. Understand concentration risk if the product relies on external models.
- Training data provenance: Is data licensed, user-consented, or proprietary? Can the company prove data rights?
- Model performance reliability: Are accuracy, latency, and failure rates documented and reproducible?
EU AI Act compliance (phased enforcement through 2027):
- Prohibitions on certain AI systems (effective February 2, 2025)
- GPAI model obligations (effective August 2, 2025)
- High-risk AI system rules (effective August 2, 2026/2027)
Map the target's AI systems to the Act's risk tiers before close. High-risk classifications carry mandatory conformity assessments, registration requirements, and ongoing monitoring obligations that the acquirer inherits.
Engineering Team, Vendor Dependencies, and Integration Readiness
Technology doesn't run itself. Assess whether institutional knowledge is concentrated in one or two individuals, and whether vendor contracts can be transferred or renegotiated.
Key-person risk:
- Identify who holds critical knowledge about architecture, vendor relationships, and system administration
- Determine if key engineers are on retention agreements or likely to leave post-close
Vendor risk is often underweighted relative to security and IP, yet contract terms and lock-in provisions can materially affect post-close integration costs and timelines.
Vendor dependency mapping:
- Cloud providers, embedded APIs, data services: review contract terms, renewal timelines, pricing structures
- Evaluate switching costs and lock-in risk (especially for AI vendors)
- Confirm transferability clauses; some contracts terminate automatically on change of control, which can disrupt operations from day one
Integration readiness:
- How do APIs, authentication systems, and data schemas align with the acquirer's existing stack?
- What middleware or custom integration will be required?
- Are there conflicting technology standards that will force rework?
The Technology Due Diligence Process: A Step-by-Step Breakdown
Technology DD typically runs in parallel with financial and legal workstreams, executed by external technical advisors, engineers, and domain specialists. Timelines range from 3–10 weeks depending on target complexity and transaction urgency.
| Step | Focus Area | Typical Timing |
|---|---|---|
| 1. Document Request | Data room setup, documentation review | Week 1 |
| 2. Technical Interviews | Leadership alignment, hidden risk identification | Week 1–2 |
| 3. Technical Assessment | Code review, architecture, security scanning | Week 2–5 |
| 4. Risk Scoring | Financial quantification, deal-breaker analysis | Week 5–7 |
| 5. Final Report | Integration roadmap, valuation inputs | Week 7–10 |

Step 1: Issue a Document Request and Establish the Data Room
The process begins with a structured request list sent to the target, covering:
- IT budgets and capital expenditure plans
- System architecture diagrams and infrastructure documentation
- Security policies, audit reports, and penetration test results
- Vendor contracts, SaaS agreements, and cloud service terms
- Software license agreements and OSS inventories
- Organisational charts showing technical team structure
All documentation is housed in a secure virtual data room to protect confidentiality and enable organised review.
Step 2: Conduct Technical Interviews with Key Leaders
Documentation alone doesn't reveal organisational maturity or hidden risks. Interviews with the CTO, CIO, IT directors, and lead engineers accomplish four critical objectives:
- Validate documentation accuracy and completeness
- Uncover undisclosed issues not reflected in written materials
- Identify where institutional knowledge is concentrated
- Assess genuine engineering maturity beyond what documents suggest
Step 3: Perform Technical Assessment and Gap Analysis
Those interview findings feed directly into the technical assessment — the investigative core of the entire process. Advisors run vulnerability scans, review code samples, analyse system performance metrics, and benchmark the target's current state against the acquirer's technical standards.
Key assessment activities:
- Static code analysis to quantify technical debt and security vulnerabilities
- Architecture review to identify scalability bottlenecks
- Performance testing under load
- DevOps pipeline maturity assessment (DORA benchmarks)
- Open-source licence audit
Step 4: Risk Score and Quantify Issues
Each identified issue is categorised by severity, assigned a risk score, and translated into financial impact — with dollar figures attached. This step separates manageable risks from deal-breakers and provides the factual basis for valuation adjustments.
Technical debt, for instance, isn't just noted — it's quantified in remediation days and estimated cost. A finding like "platform requires refactoring to scale" translates to a USD $150,000–$500,000 capital requirement with an 18–30 month break-even timeline.
Step 5: Compile the Final Report and Integration Recommendations
Findings are compiled into an executive-ready report that includes:
- Deal-breaker risks requiring immediate attention
- Detailed technical findings with severity ratings
- Estimated remediation costs by category
- Post-close integration roadmap with priority sequence
This report feeds directly into LOI negotiations, purchase price adjustments, and 100-day integration planning.
Red Flags That Can Stall or Derail a Technology Deal
Not all technology issues are equal. Some are priceable risks; others fundamentally undermine the deal thesis or expose the acquirer to undisclosed liabilities. The four categories below fall into the latter — issues that, left unaddressed, can block closing or erode value well after the transaction completes.
Disputed or Undocumented IP Ownership
If the company cannot demonstrate clean ownership of its core product—due to missing PIIA agreements, informal contractor arrangements, or overlapping claims—this creates legal exposure that can block closing.
The risk is existential: under US law, the creator owns IP unless assigned in writing. Missing assignments from founders, employees, or contractors can lower valuations, trigger indemnity demands, or require buyers to walk away entirely.
Unaddressed Security Vulnerabilities and Breach History
A pattern of unresolved security gaps or history of material breaches with inadequate response signals systemic risk. Post-close consequences include regulatory fines, customer attrition, and reputational damage.
Case study precedents:
| Transaction | Discovery Timeline | Financial Impact |
|---|---|---|
| Verizon–Yahoo | Disclosed Sept 2016 (mid-deal); breach occurred 2013/2014 | $350 million price reduction (7.25%); SEC fined Yahoo $35 million |
| Marriott–Starwood | Discovered Sept 2018 (post-close); breach began 2014 | £18.4 million UK ICO fine; $52 million FTC settlement |
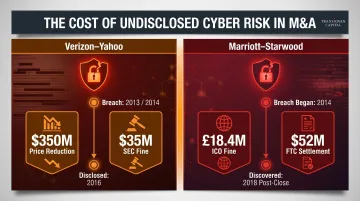
Acquirers should require independent forensic audits and contractual representations covering breach history — not just self-reported disclosures — before closing exposure is locked in.
Severe Technical Debt and Legacy System Dependency
Core systems running on outdated or heavily customized legacy infrastructure represent hidden capital expenditures. According to CAST Research, global technical debt has reached an estimated 61 billion days of remediation time across enterprise software portfolios.
In M&A contexts, technical debt remediation typically costs acquirers 15–25% of annual IT budgets over 18–36 months, eroding post-acquisition returns significantly. When these systems also lack documentation or active maintenance, integration timelines extend and cost overruns become difficult to contain.
Key-Person Dependency and Knowledge Concentration
When critical systems, architecture decisions, or vendor relationships depend on one or two individuals not under retention agreements, the buyer inherits operational risk that can compound during the transition period.
This risk is especially acute in cross-border acquisitions where talent mobility is unpredictable. Visa constraints and relocation challenges can prevent key engineers from remaining with the combined entity entirely.
How Technology DD Findings Influence Valuation and Deal Terms
Technology issues rarely kill deals outright, but they consistently move negotiating variables. Findings translate into purchase price reductions, earn-out conditions, extended representations and warranties, or specific indemnification provisions.
Purchase Price Adjustments and Earn-Outs
Over 90% of private-target M&A deals incorporate purchase price adjustment mechanisms, and approximately 22% of non-life sciences deals include earn-outs. A well-structured tech DD report enables the buyer's advisory team to quantify risk in financial terms. A finding like "significant technical debt" becomes an estimated remediation cost — one that justifies a specific price adjustment rather than a vague discount request.
For example, if diligence reveals that cloud infrastructure requires $400,000 in refactoring to support projected growth, the buyer can negotiate either:
- An upfront purchase price reduction of $400,000-$500,000
- An earn-out structure where full consideration is paid only if the platform achieves performance milestones without requiring the refactoring spend
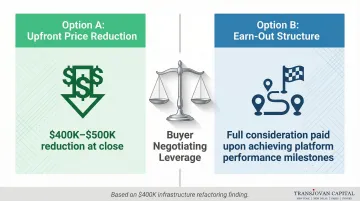
Experienced M&A advisors such as Transjovan Capital embed this risk quantification into the broader deal structure, ensuring technology findings are reflected in deal economics rather than absorbed silently post-close.
Representations and Warranties (R&W) Insurance
R&W insurance is referenced in 64% of private target deals. While claim frequency varies, 2024 saw over $300 million paid out to North American clients by Aon alone. Material technology findings often trigger specific exclusions from R&W policies or require the seller to provide separate indemnification for known tech liabilities.
R&W claim frequency by breach type (North America):
| Breach Type | % of Claims | % of Total Loss Paid |
|---|---|---|
| Compliance with Laws | 20% | 12% |
| Financial Statements | 13% | 37% |
| Material Contracts | 13% | 31% |
Technology-related breaches typically surface as compliance or material contract issues — categories that together account for 43% of total loss paid.
Integration Complexity and the 100-Day Plan
Beyond deal structure, technology findings shape what happens on Day 1. Integration complexity uncovered during tech DD directly informs the post-close 100-day plan — acquirers who know in advance which systems need immediate investment, which vendor contracts need renegotiation, and where talent retention is critical are positioned to realise synergies within the first 100 days rather than discovering blockers after close.
For instance, discovering that the target's authentication system is incompatible with the acquirer's SSO infrastructure allows pre-close planning for middleware development, vendor selection, and cutover timing. That pre-close visibility is what separates acquirers who integrate on schedule from those who spend the first quarter firefighting avoidable technical failures.
How to Prepare for Technology Due Diligence
Preparation varies by role. Buy-side teams need a clear evaluation framework. Sell-side teams need a clean, well-organized data room.
For Buy-Side Teams
- Establish a clear technical evaluation framework before diligence begins—aligned with the investment thesis
- Engage qualified technical advisors with domain expertise in the target's sector (manufacturing requires different depth than SaaS)
- Coordinate tech DD with legal and financial workstreams from the start—siloed processes lead to contradictory findings
For Sell-Side and Target Companies
Sell-side preparation directly affects how buyers perceive risk—and ultimately, how they price the deal.
- Organize a clean, well-documented data room with architecture diagrams, security summaries, IP assignments, vendor contracts, and license agreements ready
- Resolve known gaps proactively rather than waiting for buyer questions—transparency accelerates the process and protects valuation
- Consider commissioning Vendor Due Diligence (VDD) to surface and address issues before buyer scrutiny
Planning Your Timeline
Most M&A due diligence processes run 30–90 days, with the technical workstream typically spanning 4–8 weeks. Cross-border deals and targets carrying heavy regulatory burdens—healthcare providers, companies processing EU data subjects—often require 60–120+ days. Build that buffer in early; compressed timelines are where material risks get missed.
Frequently Asked Questions
What is technical due diligence?
Technical due diligence is a structured assessment of a company's technology infrastructure, software quality, security posture, and engineering capabilities. Typically conducted during M&A transactions, it validates that technology assets support the deal thesis and identifies risks that could affect valuation or integration.
What is the technology due diligence process?
The process typically follows five steps:
- Documentation collection via data room
- Technical interviews with the CTO and engineering leaders
- Technical assessment covering code quality, architecture, and vulnerabilities
- Risk scoring with financial quantification
- Final report with deal recommendations
Timelines range from 3 to 10 weeks depending on the target's complexity.
What is the due diligence process for merger and acquisition?
M&A due diligence runs multiple parallel workstreams — financial, legal, commercial, HR, and technology — each investigating distinct risk domains. Financial DD audits statements and cash flows; legal DD reviews contracts and liabilities; technology DD assesses digital assets and infrastructure. All workstreams inform deal structure collectively.
What is the difference between due diligence and risk assessment?
Due diligence is a comprehensive pre-transaction investigation across financial, legal, operational, and technological dimensions of a business. Risk assessment is narrower — a targeted evaluation of specific threats within a single domain. Due diligence encompasses risk assessment while also covering claim validation, asset quality, and strategic fit.
What is the difference between VDD and VA?
VDD (Vendor Due Diligence) is a sell-side exercise in which the target commissions its own diligence report for prospective buyers, establishing baseline facts and accelerating the process. VA (Valuation Assessment) determines the financial value of a business or its assets using methods such as comparable transactions, discounted cash flow, or asset-based approaches.
Is FDD part of M&A?
Yes. Financial Due Diligence (FDD) is a core M&A workstream focused on auditing financial statements, cash flows, working capital, and earnings quality. While distinct from technology DD, the two workstreams intersect — particularly when technology assets drive a significant portion of the target's value or when technical debt affects future cash flow projections.